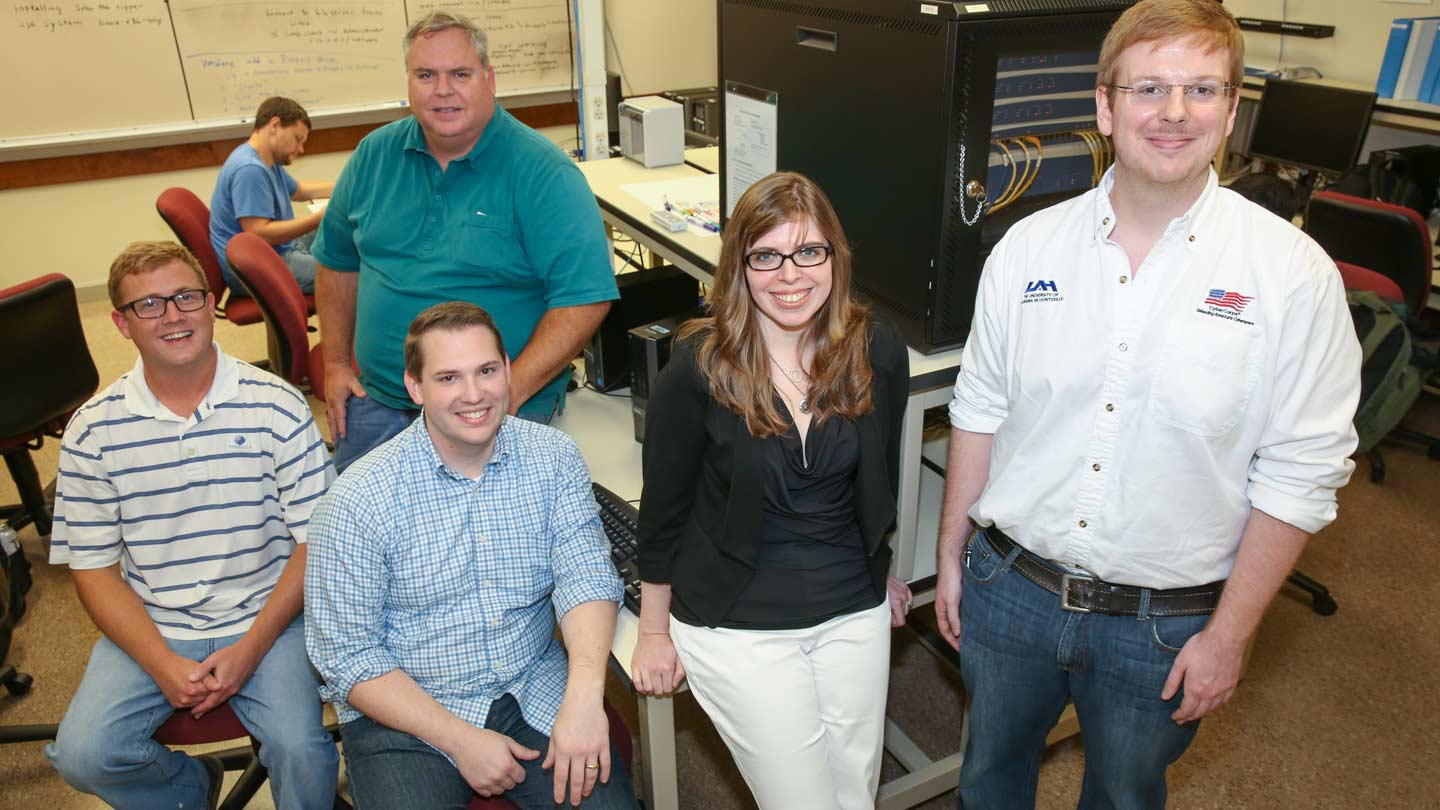
Members of the UAH cyber analysis team are, from left, David Hilsman, James Bleier, Kell Rozman, Danielle Wright and Nathan Sissom.
Michael Mercier | UAH
A University of Alabama in Huntsville (UAH) student team has qualified to be one of nine participating in the Nov. 5-7 finals of the 2015 National Cyber Analyst Challenge powered by Lockheed Martin in Washington, D.C.
By qualifying for Phase II and Phase III, the UAH team has been awarded $7,500. The Challenge's Phase III offers a $25,000 award for the winner.
The UAH team is:
- James Bleier, graduate student in Cybersecurity;
- David Hilsman, junior, Information Systems / Information Assurance concentration;
- Kell Rozman, graduate student in Cybersecurity and team lead;
- Nathan Sissom, graduate student in Cybersecurity; and
- Danielle Wright, graduate student in Cybersecurity.
"This is a great opportunity to be on stage with some of the top cybersecurity institutions in the country that include schools like Carnegie Mellon and University of Arizona, among others," says team advisor Dr. Ravi Patnayakuni, an associate professor of Information Systems in the Department of Management, Marketing and Information Systems at the College of Business Administration.
By qualifying, the team will also receive an industry mentor, training, a web-based community to engage with and learn from other schools and industry, and additional learning experiences.
"UAH was invited because of its strong presence in cybersecurity education," says Dr. Patnayakuni.
In Phase I, the UAH team successfully analyzed an incident using cyber security and forensic skills.
"Phase I of the challenge was a great learning experience since we did not have experience with performing an incident response," says team lead Rozman.
All entries were reviewed by a panel of judges and scored on technical quality, accuracy and presentation.
The team was provided with approximately 70 gigabytes of data in the form of various computer files and had to figure out how the breach occurred, the attack vectors and recommendations for preventing such breaches from occurring in the future.
"We had to organize our team quickly, as Phase I of the challenge started right before school started and we had three weeks to deliver our findings," Rozman says. "I was not sure what to expect, since I had not met anyone on the team prior, but it was immediately obvious everyone is a team player and that allowed the team to come together quickly to tackle the challenge. Once our team came together, we went to work in the cyber lab to get the computers set up for a forensics investigation."
There was no evidence of e-mail use as an attack vector but this attacker had used phishing attacks in the past, the team learned, and the FBI observed a "d.7z" file being transferred from a machine. With those clues, the team started to look at the log files.
"We learned in class that cyber attackers typically follow a 'kill chain' framework for attacking their targets," Rozman says. "With this knowledge, we went to the whiteboard and started looking through the files to piece together each piece of information identified and where it fit in the kill chain."
The team traced the file being transferred out and its associated Internet Protocol (IP) address to China. Using the same IP address, the students found the website that the security administrator accessed that caused a cross-site scripting attack.
"At this point, we thought that this type of attack was too isolated for this to be it," says Rozman. "How did the attackers know to target this individual and the kind of website he would visit? Our hypothesis was that it was a phishing attack, based on the attacker's profile."
Team members verified that the security administrator's machine was compromised and identified multiple malware files. With that information, they found the same malware file listed in an e-mail.
"With this, we finally found the main attack vector!" Rozman says. "We had a lot of data that us technical people love, but we had to distill the information to a level that a CEO would understand. We put together our information in such a way that it would convey the severity, impacts and recovery needed for a CEO to make the right decisions to move the corporation forward after the attack."